Full Report - OKTA - Defining An Industry (2/3)
At a modest valuation, there is a huge room for OKTA to continue to grow as the sector defining vendor.
This is the edited version originally from the discussion within Convequity on 30th Jun 2021,
Sources of Alpha: Complexity of the Business
Expected Price Appreciation: 110% from $220 within 3 years
Content
A brief review of the mega trends propelling Identity Management to growing importance within the cybersecurity industry.
OKTA’s CEO & Founder, Todd, McKinnon, has a grandiose and differentiated vision for the role of identity and aims for OKTA to define the industry’s standards.
Article 2
A technical dive into the progression of identity and how it works.
An assessment of OKTA’s dominance in its core IAM market and likely success entering into neighbouring IGA and PAM markets.
We view high growth, improving profitability, and gradual multiple contraction will generate market-beating investor returns over a long horizon.
IAM Competitor Analysis
IAM is a high-growth market, but in regards to innovation, is further along the maturity spectrum than other areas of identity management. All the top providers have very similar capabilities pertaining to SSO and MFA, therefore, OKTA’s investment appraisal is more about its positioning to defend its IAM moat rather than an assessment as to whether they can pull out some cutting-edge technology that the others aren’t doing.
High-Level Assessment
As a starting point to our competitor research, we referred to Gartner’s Peer Insights to gain a high-level assessment of IT admins’ experiences in working with the different IAM software. As can be seen in the following chart, 91% of IT administrators would recommend OKTA, Microsoft Azure AD, and OneLogin. Ping Identity (PING) also receives a high recommendation rate of 86%, however, ForgeRock at 81% appears to be trailing the top 3 by a noticeable margin.
Figure 3 - Gartner Peer Insights Recommendations for IAM Software
Source: OKTA, MSFT Azure AD, OneLogin, PING, ForgeRock
Convequity Primary Competitor Analysis
The binary nature of Gartner’s recommendation question doesn’t present any granularity. Of course, there are varying degrees of recommendation, therefore, we decided to read through a number of individual reviews for each company to gain more detailed insights.
The objective of this extensive research is to ascertain the risk in OKTA losing its market leading status in IAM. We compared OKTA to Microsoft Azure AD, OneLogin, Ping Identity, and ForgeRock across 12 components. We’ve read 20-40 IT admin reviews for each company from sources such as Gartner’s Peer Insights, g2.com, and IT Central Station, and also considered the findings from The Blueprint, which is a Motley Fool tech review service. The following chart shows the results of this qualitative research process. The results closely align with Gartner’s recommendation results whilst also presenting a good dose of granularity.
Figure 4 - IAM Competitor Analysis
Source: Convequity
OKTA is certainly not in a league of their own but the research strongly indicates they do have an edge over rivals. Out of the 4 competitors, we believe only Azure AD and OneLogin are capable of effectively competing with OKTA. For each company, we’ll briefly add some colour.
OKTA
OKTA’s differentiation mainly relates to the ‘Ease-of-use’ component. This component encapsulates the ease that IT admins experience when deploying and managing the IAM software. We only found a couple of negative reviews pertaining to OKTA’s ease-of-use and these were more than 2 years old. We surmise the comparative ease of using OKTA can be attributed to the platform-agnostic nature and the extent in which the open standards protocols (OAuth, OpenID, and SAML) are present within the software. And by being cloud-native, OKTA’s software isn’t entangled with legacy proprietary protocols that make things complicated.
OKTA’s edge in security is minor but noteworthy. OKTA has an AI/ML-infused threat intelligence platform called ThreatInsight that is continually improving thanks to the volumes of data its receiving from OKTA’s 10,000 customers. Combining this with OKTA’s zero-trust and MFA is proving to be highly effective in strengthening security postures.
OKTA scores strongly across all areas, however, criticism was mainly directed toward the cost. The expense of OKTA is a downside for businesses but an upside for investors because it indicates the management are extracting the full value of its premium software, therefore, this shouldn’t be a major concern. OKTA’s customer support appears to be fairly strong but isn’t receiving the same high praise as PING’s and ForgeRock’s. We infer that that PING’s and ForgeRock’s customer support is highly responsive to compensate for shortcomings in other areas.
OneLogin
OneLogin’s main weakness versus OKTA is the breadth of features. This is probably due to the OKTA’s greater size affording them to make bigger R&D investments. We’ve also found that OneLogin trails OKTA in ease-of-use and customization by a noteworthy margin. OKTA’s reportedly more streamlined user experience is another edge over OneLogin.
On the whole, however, we would say OneLogin and OKTA are in the same bracket. But what’s important to note as a potential OKTA investor, is that OneLogin doesn’t have any material competitive advantage, despite being the closest rival.
Microsoft Azure AD
The main areas in which MSFT trails OKTA by a significant margin are ease-of-use, integrations, and price transparency. Expressed both explicitly and implicitly, IT admins often feel overwhelmed operating Azure AD within the vastness of the Windows ecosystem. As a result, maximizing the potential of Azure AD can be a little daunting, especially for non-expert Windows administrators. In contrast, as OKTA focuses solely on IAM, navigation tends to be easier for IT admins.
Compared to Azure AD, OKTA has more than double the available app integrations (Workday, Salesforce, ServiceNow, Zoom, etc.). This is because OKTA is platform-agnostic, whereas Azure AD only interacts with Windows and Linux operating systems, and, overall has a bias to limit integrations in order to protect their ecosystem. This makes Azure AD less adaptable to future landscape changes – we’re already seeing Apple rapidly gain market share in business OS environments. Therefore, should Windows continue to concede OS market share, OKTA has a significant long-horizon upper hand over Azure AD.
Lastly, given the innumerable permutations of Windows packages including Azure AD, working out the end cost tends to be confusing, which is why Azure AD scores moderately in this component. However, Azure AD is often thrown in as a freebie as part of a larger business package, therefore, it scores highest in terms of cost.
There is much granularity in the differences between OKTA and Azure AD, but the high-level takeaway is that we believe OKTA will outplay MSFT in the identity space over a long-horizon. As we’ve mentioned in prior reports, identity is rapidly growing in importance amid the cybersecurity landscape, and with this in mind, OKTA’s identity-centric and platform-agnostic business strategy should yield better long-term results than MSFT’s business strategy wherein identity is a small part of a bigger whole. In fact, OKTA’s CEO & Founder, Todd McKinnon, has recently stated that OKTA’s strategic objective is to make identity the primary cloud – meaning that identity should be the core of digitally-enabled business operations, not peripheral. Within the current context, we feel this is a powerful strategy to outcompete MSFT in IAM and the broader identity space.
Ping Identity
PING trails OKTA by a wide margin in all components except for customer support. PING’s target market is the large enterprise, usually with hybrid computing environments. PING is adjusting to the cloud to deliver SaaS IAM, though they have a long way to go. As a consequence, there is little self-serve available to clients, so deployments necessitate a lot of deployment support from PING and System Integrators alike. Because of PING’s shortcomings as it pertains to SaaS delivery (including its extent of utilizing Software-Defined Networking), customer support is critical for its survival, which is why they score particularly well for this component.
A telltale sign as to whether or not a software provider is sufficiently SaaS and SDN-oriented is the pricing page on their website. Providers that are still overly entangled in legacy infrastructure and protocols will have only a ‘Request for Pricing’ or ‘Contact Sales’ message on their pricing page. Cloud-native, and most importantly, SDN-oriented providers, are able to offer transparent pricing structures as they have greater levels of abstraction throughout the tech stack, thereby making them more conducive to the elastic nature of cloud computing. PING’s pricing page definitely confirms they are lagging in cloud transformation.
PING’s legacy roots weighing them down was blatantly evident during the depths of the pandemic. In Q2, Q3, and Q4 of 2020, PING experienced YoY declines in revenue as it manifested that they weren’t able to scale their software to meet the new demands of the market. And in Q1 of 2021, YoY growth has only recovered to 12% within a high-growth industry. Additionally, PING’s dollar-based net retention rate of 109% versus OKTA’s 121%, is another indicator that they are a struggling business.
The jump in PING’s R&D as a percentage of revenue (23% in 1Q19, 17% in 1Q20, and 31% in 1Q21) suggests they acknowledge that they weren’t agile enough to handle COVID-19 and are now playing catch-up. However, their slowness has likely caused an irreversible gap between themselves and OKTA, so we don’t see them as a credible threat.
ForgeRock
ForgeRock score relatively lower across most of the 12 components, especially in regards to ease-of-use and features breadth. We saw a few IT administrator reviews complaining about there being excessive bugs throughout the software, which they attributed to its Sun Microsystem origins. When Sun Microsystems was acquired by Oracle in 2009, six Sun employees resigned and then founded ForgeRock in 2010, and built the code using Sun’s open-source software. Sun’s open-source software was phased about by Oracle in favour of an in-house alternative, therefore, its developer community dwindled. By connecting the dots, it appears that subsequently interoperating open-source OAuth and OpenID with what turned into closed Sun software, is the cause of excessive bugs and a disappointing IT admin experience.
Like PING, ForgeRock also has no pricing available to view on its website – a clear sign that they are not leading SaaS/SDN providers. With all this in mind, despite the sizeable VC investments into ForgeRock, we don’t see them as a threat to OKTA’s IAM domination.
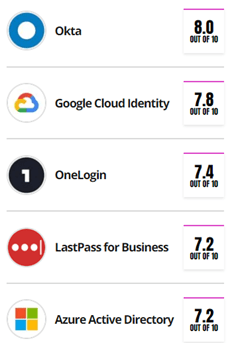
Secondary Competitor Analysis
Just in case the reader perceives a possible confirmation bias given we’ve already spent many hours researching OKTA and have already opened a 5% position, below we present the findings from Motley Fool’s tech review service called The Blueprint. Whilst the provider selection is different to our own, the main takeaway is that OKTA is a cut above OneLogin and Azure AD.
Figure 3 - The Blueprint: A Motley Fool Service
Source: fool.com/the-blueprint/okta-review/
IAM Summary
The purpose of this section was to ascertain the risk of OKTA losing share of its core market to its closest IAM rivals. We conclude that the probability of OKTA being outcompeted is very low. OKTA’s cloud-native architecture is completely free of legacy overhang that is a huge factor in making things easy for IT administrators and ultra-streamlined for users. On the contrary, legacy entanglement makes it difficult for PING and ForgeRock to deliver these benefits to the same extent as OKTA can.
MSFT is a strong IAM competitor, though the lesser integration capabilities put Azure AD at a disadvantage, especially when considering Apple’s rise in the business environment.
OneLogin is the strongest rival, in our opinion, however they don’t have a niche capability that can slowdown OKTA’s momentum and weaken their moat. And actually, OKTA does appear to have the edge over OneLogin in arguably the three most important areas – IT admin ease-of-use, security, and user experience.
OKTA vs SAIL
SailPoint (SAIL) sell Identity, Governance, & Administration, or IGA, software, and as we discussed in the Initial Thoughts report, in Apr-21, OKTA announced their entrance into the IGA market with a full suite of offerings. It was a big announcement; however, OKTA had been testing the water for about 12 months prior with an IGA solution called Lifecycle Management which relates to the adjustments to access and authorization throughout an employee’s or contractor’s tenure at an organization.
Figure 4 - Identity Lifecycle Management
Source: ldapwiki.com
Therefore, to conduct a loose like-for-like comparison, we read numerous Gartner Peer Insights reviews for OKTA’s Lifecycle Management solution and for SAIL’s Identity Platform. Firstly, however, we reviewed the overall recommendation results as we did for IAM. As can be seen, despite being a younger product, OKTA’s IGA (whilst having a narrower scope) has a significantly higher recommendation rate.
Figure 5 - Gartner Peer Insights Recommendations for IGA Software
At first take, last-mover advantage instantly sprung to mind. Despite being less experienced, thanks to their microservices architecture and SDN approach, OKTA has entered the IGA space with what is regarded as a better solution than a long-established legacy market leader.
From reading 15-25 reviews for each product, it became abundantly clear that implementing SAIL’s solution requires substantial third-party consultancy and/or System Integrators along with highly skilled and experienced IT admin personnel. The breadth of SAIL’s IGA is formidable, however, specialist IT administrators are required or there is a long and steep learning curve to embark upon. Many reviews recommended others to recruit IGA experts and commit to intensive training before making the decision to implement the software.
The resource requirements for implementation combined with their quote-based pricing highlights that SAIL is far from being a cloud-based company capable of delivering true SaaS.
The main positives in using SAIL’s IGA pertained to its customizability, audit/reports, and the automation features. During 2020, SAIL performed better than PING – growing revenues YoY by 24%, 47%, 24%, and 16% in Q1, Q2, Q3, and Q4 – though this was because SAIL is the outright leader in IGA. PING’s legacy infrastructure hurt them more during the pandemic because the alternative for customers was OKTA’s SaaS-delivery IAM solution. Fortunately for SAIL, they didn’t have a formidable SaaS alternative directly competing with them – however, they do now.
Comments about OKTA’s IGA (Lifecycle Management) that appeared a few times related to its easy onboarding, extensive integrations, flexible configurations, intuitiveness, customization, and super-fast response times when applying settings – attributes all facilitated by a cloud-native solution.
After reading through the reviews, we listened to an interview with SAIL’s CFO, Jason Ream, at the Cowen Technology, Media and Telecom Conference on 3rdJune 2020. Ream pretty much completely dismissed OKTA’s chances of success in IGA – probably expected really. He mentioned how SAIL’s enterprise customers said they couldn’t see a use case for OKTA’s Lifecycle Management solution and that is an inkling that OKTA isn’t really vying for the same type of customers. However, if you check the reviews you’ll see many large companies purchased and implemented OKTA’s Lifecycle Management during 2020 and thus far into 2021. And those customers highly rate the solution. Such a misleading remark by Ream coupled with his overall unconvincing take on OKTA’s venture into IGA leads us to believe he was hiding his true feelings – which, of course, would be expected when talking about any rival.
SAIL has been slowly adapting to a SaaS-delivery model, and this can be construed by the recent declines in gross margin shown in the table below. SaaS providers pay the public clouds for the elastic computing infrastructure, hence upon the early stages of a cloud transformation the cost of revenue will likely increase. The same pattern has occurred with PANW since they’ve adjusted to deliver SaaS. When a certain volume of traffic is reached, however, cost of revenue % within a cloud environment should decline, thereby increasing a hybrid provider’s overall gross margin to an extent. We think PANW is probably at this juncture as its gross margin has stabilized and management have guided an increase over the next few years.
On the other hand, given SAIL’s low proportions of revenue coming from SaaS at present, we suspect its gross margin could decline further from here before eventually reversing.
Figure 6 - SAIL's Recent Gross Margin
Thus far we’ve made a strong case that OKTA’s newly launched IGA can outcompete SAIL’s. We think it’s an opportune time to reshow the findings from the ETR research that we presented in OKTA’s Initial Thoughts report. The chart shows that 35% of SAIL’s customers also have an OKTA account. The preexisting relationships combined with a better SaaS-alternative, brings us to believe OKTA’s chances of success in this c. $8bn market are very high.
Figure 7 - Customer Accounts Using OKTA with SailPoint or CyberArk
Source: wikibon.com
Relative valuation-wise, we also like the look of OKTA versus SAIL. NTM EV/S for OKTA and SAIL are 27x and 11x, respectively, and given OKTA’s 10x greater TAM, 2x TTM revenue, 4x growth, better technology, and more effective business strategy, we view the relative premium as fair, or even a good bargain.
Below we present the relative valuations adjusted for gross profit. Given gross margins are in the same bracket, the outcome is the same as the previous NTM EV/S consideration – OKTA’s valuation is 2.5x richer than SAIL’s. However, we reiterate that this seems like a premium worth paying.
Figure 8 - Relative Valuation: OKTA vs SAIL
Source: Convequity
OKTA vs CYBR
The competitive dynamics between OKTA and CyberArk (CYBR) are very similar to OKTA vs SAIL, whereby OKTA is entering an identity space, primarily dominated by on-prem solutions, with a SaaS-based alternative.
CYBR is the long-established leader in Privileged Access Management, aka PAM, which pertains to protecting administrator and other highly privileged company accounts from being compromised. CYBR primarily delivers on-prem solutions whilst making some adjustments to also deliver for cloud environments. OKTA has its SaaS-based Advanced Server Access (ASA) solution that has been in existence for about 18 months, which lays the foundation to the launch of their full PAM suite scheduled for early 2022.
We found lots of reviews on CYBR’s PAM solution but couldn’t find any for OKTA’s ASA solution. Therefore, we’ll briefly summarize the feedback from IT administrators that have used CYBR’s product (to check the reviews yourself click the link).
Firstly, 83% of IT administrators recommend CYBR – which is similar to SAIL’s and PING’s. Most of the reviews indicate high satisfaction with the end results of heightened security and better organization surrounding privileged accounts, but express frustration with the means of getting to a secure state and the ongoing management. Many administrators cite the excellent password management and other security functionality for securing local admin/root accounts but explain that CYBR is not an out-the-box solution and that substantial time and expertise is required in order to get the software operational. On the whole, very similar feedback to SAIL’s.
When using CYBR, IT admins need to manually provision new servers and root accounts, which is a time-consuming process, especially working for large enterprises that need to regularly change computing resources. This is one of many headaches that OKTA’s PAM solution will resolve. OKTA is deployed in AWS and hence gives customers autoscaling and provisioning benefits.
CYBR is even further behind in the cloud transformation than SAIL. YoY quarterly growth since the pandemic has ranged from -2% to 11%. The poor growth is directly attributable to their term license, on-prem business being unable to scale and meet the COVID-induced demands. They do have some SaaS business, but in a similar vein to SAIL and PING, legacy entanglement is bogging down its potential.
If OKTA can produce a comparable full PAM suite that is SaaS-delivered and do it in a timely manner, then they will easily outcompete CYBR and dominate this $7bn market. Legacy PAM solutions have narrow feature sets for dealing with DevOps workflows involving containers and functions-as-a-service etc., so greater cloud adoption will eventually marginalize their role – another positive trend for OKTA.
CIAM
The Customer Identity & Access Management (CIAM) is relatively nascent and hence reviews are hard to find. Therefore, we’ve not conducted a thorough competitor analysis and will instead focus on OKTA’s strategy and opportunity ahead. We have gleaned that some of OKTA’s IAM rivals – OneLogin, ForgeRock, and PING – are dabbling in CIAM, but don’t have anything that compares with Auth0, which was acquired by OKTA in Mar-21.
Compared to IAM, CIAM has different market needs and dynamics. IAM can be delivered as SaaS because there are lesser requirements for customization within workforce identity – employees simply just want easy access to the apps/systems to be productive in their work. CIAM, on the other hand, needs to have an element of PaaS (Platform-as-a-Service) for greater customizability and extensibility given that customer identity is becoming increasingly intertwined with CX (preferences, content, etc.), privacy (consent, GDPR, etc.), and marketing (adverts, emails, etc.), in unique ways and across an omnichannel environment. It’s become so much more than simple access.
OKTA has a home-grown CIAM product that’s based on a low-code format. This is an approach that reduces the amount of custom coding required to build an application by incorporating drag-and-drop interfaces, reusable code templates, and software development kits (SDKs) into the software development process. It helps make app development faster by providing developers and non-developers prebuilt sections to assemble instead of coding every line.
Auth0’s developer platform is way more advanced in that it provides low code and more sophisticated customization options. Auth0 aims to help companies deliver highly secure, enriching, but invisible SSO experiences for its users. If you have the time, to fully grasp how cutting-edge Auth0 is you should the InterMiles case study. If you don’t have the time then just digest the following summary.
InterMiles is a travel and lifestyle rewards program that wanted to create not just a SSO experience across their own multiple sites, but also across its various independent partner sites, so its members can move freely between sites while remaining authenticated. They also wanted to leverage social profiling and partner data to customize each user’s journey with InterMiles. To add to the challenge, as such reward program sites are high value targets for cybercriminals, they required an ultra-secure solution. Other issues included InterMiles having an on-prem CRM system that couldn’t scale to meet the SSO demands they wanted, and they also had a policy preventing any external SaaS vendor from accessing their proprietary source code.
Following a tender involving 15 vendors, InterMiles selected Auth0 for their proposed solution, expertise, and timeliness in delivering the project (Auth0 could deliver in weeks vs the comp. that needed months). Auth0’s solution included:
Member initiated SSO from any partner, with sessions persistent across all sites.
Social profile data integration to streamline login experience and enhance account management.
Securely enabling partners to access members’ data in the InterMiles databases.
Integrating SSO into the on-prem CRM system.
Auth0 became the identity provider for every member login and partner access.
Auth0 collaborated with a third-party development team to lay Auth0 on top of InterMiles proprietary source code without gaining access.
The highest security standards built into every facet of the new system.
As evident in the InterMiles case study, Auth0 is certainly pushing the boundaries of customer SSO. OKTA’s SaaS-delivery model, customer base, and sales force combined with Auth0’s developer-centric platform offers up plenty of revenue opportunity.
Auth0’s CEO & Founder, Eugenio Pace, has explained how Auth0 often lands inside an enterprise thanks to one developer who has opened a free plan account. From there, adoption grows and developers champion Auth0 until it’s considered by higher-level executives for large scale projects. This scenario is ideal for OKTA’s sales force to target these free plan accounts with a high-touch, top-down approach and expedite the land & expand process.
The following diagram illustrates this developer-seeded scenario combined with the cross sell and upsell opportunities across customer and workforce identity alike. Interestingly, McKinnon explains that the $30bn customer identity (CIAM) market will have a mix of needs, some of which can be served by OKTA’s low-code platform, and more complex needs that will need Auth0. Acquiring Auth0 will transpire to be a good move because otherwise OKTA will have missed out on a lot of business whereby the enterprise wants to build something in-house that is highly customized from the ground-up. Auth0 offers an easy-to-use platform to do this.
In effect, following the Auth0 acquisition, OKTA has sandwiched the customer identity market from side-to-side with the low-code and Auth0 solutions (non-expert and expert), and also sandwiched the top and bottom of the market with enterprise project sales and developer-initiated free plan accounts, respectively.
Figure 9 - OKTA's Market Opportunities
Source: Convequity
Evolution of CIAM
CIAM systems implemented like InterMiles’ will greatly enhance customer experiences whilst strengthening organizations’ security posture. Though CIAM’s role isn’t going to stop here. CIAM will likely become core to the CX (customer experience) evolution, seamlessly interoperating with other technologies and business functions to augment customer engagement.
Identity systems collect huge volumes of data that is traditionally analyzed by security professionals to defend against cyberthreats and respond to incidents. However, increasingly this data can be used to assess user behaviour patterns, such as:
how they interact with mobile apps and the website,
how long they take to register,
preferences tied to privacy,
how long it takes for their issues to be resolved by customer service (call centre, live chat, etc.),
the ease they experience when resetting passwords etc.
All this data can be used to redesign apps, websites, and customer service channels to better streamline user experiences, offer greater personalization and targeted marketing, and more efficiently adhere to data privacy regulations. This results in greater user satisfaction >>> greater engagement >>> greater revenue, all whilst optimizing business operations and remaining compliant.
Basically, CIAM is going to connect and enhance various other business functions and form the core of customer management platforms.